In part 4 of this series I configured Microsoft Exchange to work with nginx.
In part 4 of this series I configured Microsoft Exchange to work with nginx.
In this final part of the series I tidy up the loose ends so it can be put live.
Other articles in the series:
- Installing and configuring keepalived
- Installing nginx+
- Configuring nginx+ for Microsoft Exchange
- Configuring Microsoft Exchange
- Tidying up
The first thing to configure is synchronise the nginx+ configs between both VMs. To do this we will use rsync over SSH.
Create a new user on both VMs to run the rsync copy. Insert your own password as desired:
useradd -s /bin/bash -p $(echo mysecretpassword | openssl passwd -1 -stdin) sa_copyconf
On HA1, login as the user and create the SSH keys:
mkdir .ssh
chmod 700 .ssh
cd .ssh
ssh-keygen -t rsa -N '' -b 2048
Accept the default file name for the private key. Add the public key to the list of authorized keys:
cat id_rsa.pub > authorized_keys2
chmod 644 authorized_keys2
Copy the public key over to HA2:
cat id_rsa.pub | ssh ha2.mail.mdb-lab.com "mkdir .ssh && chmod 700 .ssh && cat > .ssh/authorized_keys2"
On HA2, login is as sa_copyconf and set the permissions to /home/sa_copyconf/.ssh/authorized_keys2:
chmod 644 /home/sa_copyconf/.ssh/authorized_keys2
Also on HA2, copy across the id_rsa file from HA1 and place in .ssh:
sftp ha1.mail.mdb-lab.com:.ssh/id_rsa .ssh/id_rsa
On each VM, add permission to /etc/nginx/ for sa_copyconf:
setfacl -m u:sa_copyconf:rwx /etc/nginx/
Next, install rsync (if it isn’t already):
yum install rsync -y --nogpgcheck
Create the following script on each host (replace the hostname as needed – on HA1, it should reference HA2 and vice-versa):
cat <<EOF> /home/sa_copyconf/copyconf.sh
#!/bin/bash
rsync -avuz -e ssh ha2.mail.mdb-lab.com:/etc/nginx/nginx.conf /etc/nginx
EOF
Make the script executable:
chmod +x /home/sa_copyconf/copyconf.sh
Add a cron job to run the script every five minutes:
crontab -l | { cat; echo "*/5 * * * * /home/sa_copyconf/copyconf.sh"; } | crontab -
To test, delete the config on HA2:
rm -f /etc/nginx/nginx.conf
Wait ten minutes and the config should now reappear on HA2. To check this:
diff /etc/nginx/nginx.conf <(ssh ha1.mail.mdb-lab.com 'cat /etc/nginx/nginx.conf')
Next, restrict VRRP (the protocol keepalived uses) to the IPs of the two hosts. On HA1:
iptables -D INPUT -p 112 -j ACCEPT
iptables -I INPUT -p 112 -s 172.17.80.12 -j ACCEPT
service iptables save
On HA2:
iptables -D INPUT -p 112 -j ACCEPT
iptables -I INPUT -p 112 -s 172.17.80.11 -j ACCEPT
service iptables save
Test this by pausing the VM currently owning the cluster addresses and verifying they have transferred.
Finally, SELinux needs to be modified so nginx can run. To demonstrate this, enable SELinux:
setenforce 1
Then restart the nginx service:
service nginx restart
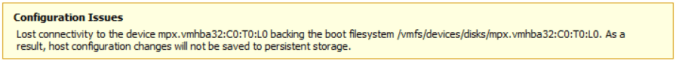
You will get the following error:
nginx: [emerg] bind() to 172.17.80.13:135 failed (13: Permission denied)
nginx: configuration file /etc/nginx/nginx.conf test failed
This is because with SELinux enabled nginx is unable to bind to tcp/25, tcp/135 and tcp/139. To work around this:
grep nginx /var/log/audit/audit.log | audit2allow -m nginx > nginx.te
grep nginx /var/log/audit/audit.log | audit2allow -M nginx
semodule -i nginx.pp
To test, restart the service again:
service nginx restart
nginx should now start without issue. On each VM run the following as root:
sudo sed -i "/SELINUX=permissive/c\SELINUX=enforcing" /etc/selinux/config
I would like to thank the technical guys at Nginx for help with the SELinux component. More information regarding this can be found on their blog at http://nginx.com/blog/nginx-se-linux-changes-upgrading-rhel-6-6/.
Nick Shadrin at Nginx has also put together a comprehensive Exchange configuration guide on their site. I highly recommend checking it out – http://nginx.com/blog/load-balancing-microsoft-exchange-nginx-plus-r6/.
Now that mainstream support for Microsoft Threat Management Gateway 2010 has ended (extended support is available till 14 April 2020), there is an opportunity to leverage technologies such as nginx+ to load-balance and publish Microsoft Exchange 2013 externally when the time comes. If there is, I’ll be sure to document it!
In this article we have provided a method of syncing the configs, tightened security and re-enabled SELinux.
That completes the series on how to configure nginx+ to load-balance Microsoft Exchange.
51.507351
-0.127758